My Blog Posts
List of my Blog posts:
2026
Why Most Embedded Software Is Overcoupled - And How Dependency Injection Fixes It
Most embedded bugs aren’t hardware problems. They’re design problems , born from code that grew organically across board revisions, tightly knotted around pin numbers, register addresses, and brittle HAL calls scattered everywhere and with scalability things can get messy, adding to the technical debt. Its important we talk about how not to make your embedded software tightly coupled and leave room for extension & scalibility Continue reading Why Most Embedded Software Is Overcoupled - And How Dependency Injection Fixes It
Local First, Building Portable Embedded C++ pipeline with self-hosted CI
How Woodpecker CI, Cosmopolitan, and Google Pigweed give small firmware teams automated build-test-flash pipelines Continue reading Local First, Building Portable Embedded C++ pipeline with self-hosted CI
The Embedded Engineer's Second Brain: PARA and CODE Systems
More information is not equal to more clarity, Here I have assembled a simple guide to turning information overload into clarity using Tiago Forte’s the CODE and PARA methods. Continue reading The Embedded Engineer's Second Brain: PARA and CODE Systems
Portable and Secure C- A Practical Guide to MISRA C & CERT C
The C language has powered satellites, pacemakers, and aircraft flight computers for five decades. That longevity is not accidental, and neither is the discipline required to keep it safe. Continue reading Portable and Secure C- A Practical Guide to MISRA C & CERT C
Binary Search Tree in C
A complete guide to Solve the Binary Search Trees(BST) Problems in C & popular LeetCode BST problems Continue reading Binary Search Tree in C
2025

Automating Hardware Testing with Python
Good measurement is extremely essential in testing, because acquired data drives key engineering decisions. While engineers prefer automated testing to minimise human error and accelerate the process of data acquisition. But automated testing is not all about running scripts on a loop. If not checked, automated testing can introduce incorrect conclusions and poor engineering decisions Continue reading Automating Hardware Testing with Python
Performance cost: std::allocator vs std::pmr::polymorphic_allocator
This blog post explores why memory management is a critical bottleneck in embedded systems and how C++17’s Polymorphic Memory Resources (PMR) compare to the default std::allocator in performance, determinism, and memory efficiency. (See correction notice - original results were flawed.) Continue reading Performance cost: std::allocator vs std::pmr::polymorphic_allocator
7 C++ Inheritance pain-points Rust Fixes Forever
Seven ways C++ inheritance can create issues, and how Rust’s composition model fixes them all. From diamond problems to fragile base classes, see why composition wins in the long run. Continue reading 7 C++ Inheritance pain-points Rust Fixes Forever

From Regulation to Implementation- Understanding Vehicle Cybersecurity legal Compliance & How Vehicle Cybersecurity Actually Gets Done
UNECE R155/R156 are regulatory requirements for vehicle cybersecurity and software updates, while ISO 26262 (functional safety) and IEC 62443 (industrial/IoT cybersecurity) are technical standards. The relationship is that UNECE mandates compliance at a regulatory level, and ISO/IEC standards provide the engineering frameworks and evidence manufacturers use to demonstrate compliance Continue reading From Regulation to Implementation- Understanding Vehicle Cybersecurity legal Compliance & How Vehicle Cybersecurity Actually Gets Done
RAII in C++ vs Rust- How Each Language Manages Resources Without the Garbage collector
Managing memory and resources like files, network connections, or locks is essential in programming. While some languages rely on garbage collectors for automatic cleanup (Java), C++ and Rust use RAII (Resource Acquisition Is Initialization) to handle this deterministically. Continue reading RAII in C++ vs Rust- How Each Language Manages Resources Without the Garbage collector
Pytest for Embedded Developers- Reliable, Maintainable Test Design
Embedded Software testing used to be dominated by only C or C++ with a bit of bash scripts, however in recent times the framework of firmware and embedded-software testing has been changing rapidly integrating Python’s flexibility & ease of usage, with the CI/CD integration the testing has never been faster & secured Continue reading Pytest for Embedded Developers- Reliable, Maintainable Test Design
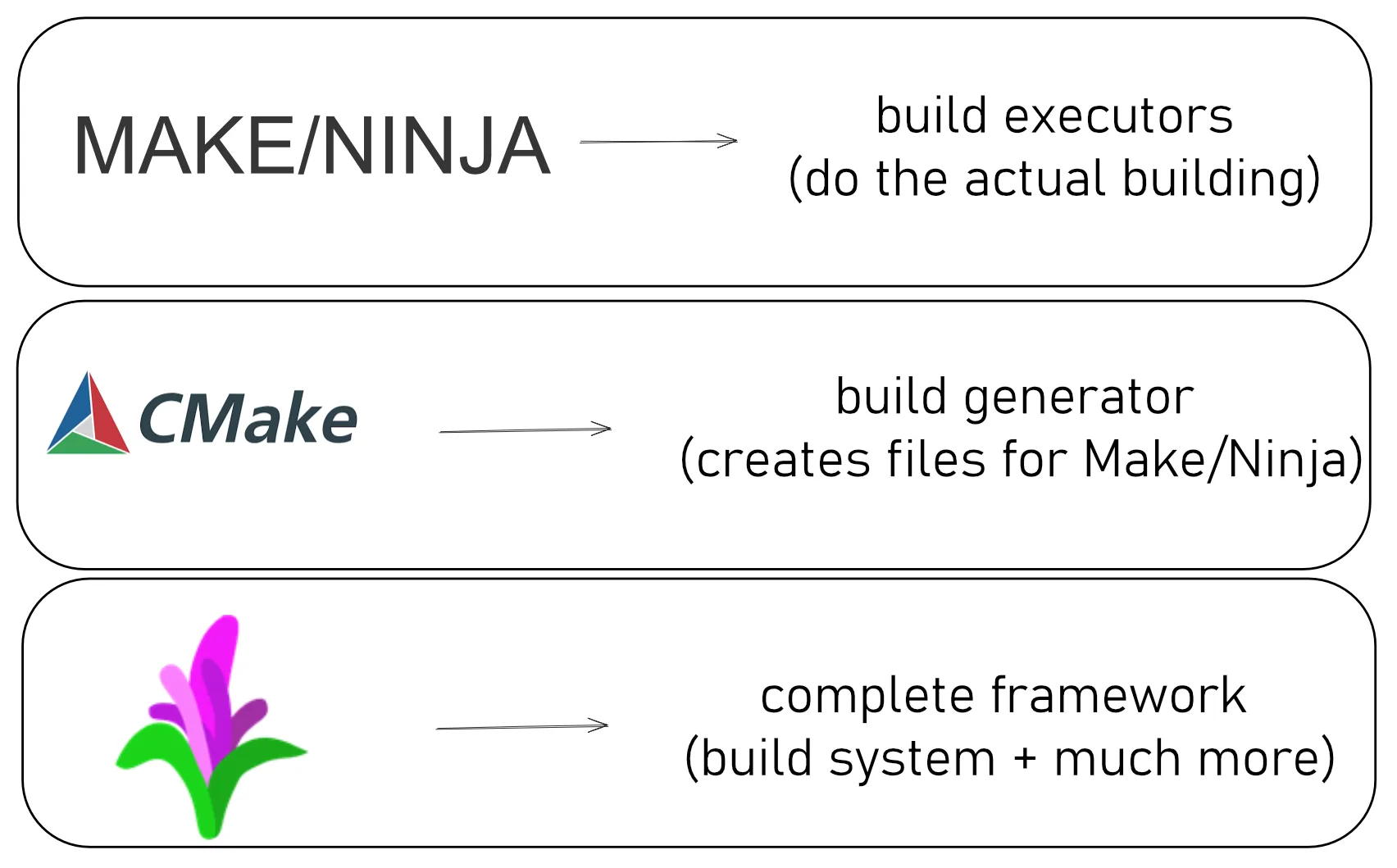
Build Systems in Embedded Development: From Make to Pigweed
Why does your code compile on your machine but fail on your teammate’s? Explore Make, CMake, and Pigweed—the tools that turn scattered C++ files into working firmware. Learn which one you actually need and why that answer might surprise you. Continue reading Build Systems in Embedded Development: From Make to Pigweed
C++ String Operations
C++’s for String Puzzels Continue reading C++ String Operations
Rust’s Borrow Checker: How It Prevents Memory Bugs (and Where You Still Need to Be Careful)
The borrow checker was the most confusing thing I encountered as a Rust beginner coming from C++. It looked like a compiler plus linter at first, but I was wrong. Here I explore how to understand and use it to grasp Rust’s design philosophy Continue reading Rust’s Borrow Checker: How It Prevents Memory Bugs (and Where You Still Need to Be Careful)

The industry of Web3.0 and Decentrelised Internet
How Web 3.0 and decentralized internet concepts can address IIoT’s challenges with centralized trust, data ownership, and scalability Continue reading The industry of Web3.0 and Decentrelised Internet

Lesser Known Fermented Drinks From Rural India
Exploring the hidden gems of India’s rural fermentation traditions - from rice beers to palm saps, these drinks tell stories of ancient wisdom and community spirit. Continue reading Lesser Known Fermented Drinks From Rural India
Bitwise Operations in C/C++
A comprehensive guide to bitwise operations in C and C++, covering operators, practical applications, and common patterns for efficient programming. Continue reading Bitwise Operations in C/C++
